This tutorial walks you through the steps to add and manage accounts and users.
Before you start
Before you start this tutorial, some things to understand:
- Pro or Enterprise edition is required
- This tutorial will be easier if you first have a basic understanding of:
- This presents one recommended workflow but no particular order of steps is required.
Tip
We recommend that you consider implementing domain capture that lets you automatically add users to your organization based on their email domain. This prevents users from accidentally signing up for New Relic and creating an unnecessary and unwanted New Relic organization. This feature is available for Pro and Enterprise accounts.
Overview
This tutorial walks you through the logical RBAC setup workflow:
- Organization creation
- How to add accounts
- How to set up an authentication domain
- How to create groups
- How to create custom roles
- How to create access grants
- How to add users
Organization creation and setup
When you sign up for New Relic, your New Relic organization is created. The organization structure represents a New Relic customer: it's what contains everything relevant to a customer's use of New Relic: their accounts, their users, and their data.
When a New Relic organization is created, it contains a single account. Pro and Enterprise edition organizations can add more accounts.
When your organization is created, it has two default user groups, which have roles and accounts already assigned. When you add users via the UI, there are two default groups you can assign users to:
Admin: can use and configure observability features for that initial account, and the ability to view and configure organization-wide administration settings (like adding accounts, managing authentication settings, and adding/removing users).
User: can use and configure observability features (but lacks access to the admin abilities that the Admin group has).
You can see the access assigned for these default groups by going to the Access management UI:
Log in to one.newrelic.com.
Click your user name, then Administration > Access Management.
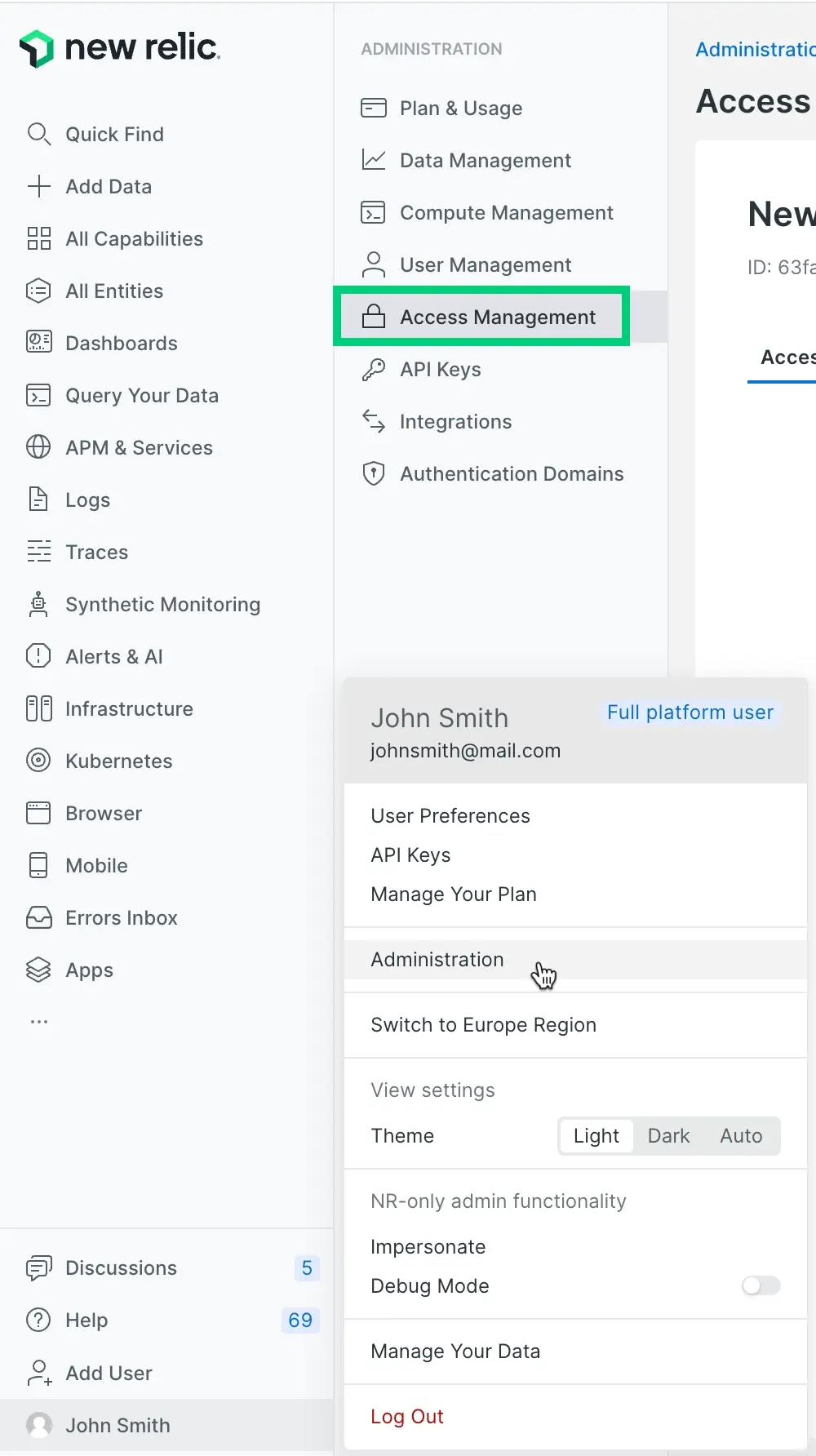
You can see how the User group has the All product admin role and access to that initially created account. And you can see how the Admin group has some administration settings assigned. The
Defaultnext to those group names refers to them being in the original, default authentication domain.If you want to create admins who can only add and remove users, and who don't have the more powerful organization-wide admin capabilities that the Admin group has, you can use the Group admin role.
Add accounts
Before adding your users in New Relic, you might want to get some data reporting and set up additional accounts.
For reasons why you might want to create more accounts, see Organization structure.
For how to add accounts, see Add accounts.
Set up authentication domains
When your organization is first created, the groups and users are located in a default authentication domain, named Default. An authentication domain is a grouping of New Relic users governed by the same user management settings, like how they're provisioned (added and updated), how they authenticate (log in), session settings, and how user upgrades are handled.
The default authentication domain settings are:
Users are manually added and managed via the New Relic UI
Users manually log in to New Relic using their email and password
Having that single domain will be fine for many organizations, but some larger organizations want one or both of the following:
Single sign-on (SAML SSO)
Managing their users from their identity provider via SCIM provisioning
If you need single sign-on or SCIM provisioning, you'll have to create an additional authentication domain. Note that groups and users are contained within authentication domains, and you can't easily change an authentication domain's provisioning setting or authentication setting once the domain is created: this means you should spend some time thinking about what your authentication domain settings should be before you add users to them.
If you want to use SAML SSO or SCIM provisioning, see these options:
Create groups
Groups are containers for users that determine what access those users have through access grants. You can use the default Admin and User groups, or create custom groups for more specific access patterns.
To create and manage groups:
From the user menu, click Administration > Access Management.
Click the Groups tab.
You'll see the default groups (Admin and User) that are automatically created with your organization.
To create a new group, click + Add a group.
In the Create a group modal:
- Enter a Group name
- From the Authentication domain dropdown, select the authentication domain for this group
- Optionally add users to the group using the Add users dropdown
Tip
You don't need to configure group access here - that happens later through access grants. The groups you create are containers for users.
Consider creating groups based on:
Team structure (Engineering, Marketing, Sales)
Access levels (ReadOnly, Developers, Admins)
Geographic regions (US-East, Europe, APAC)
Project teams (Project-Alpha, Project-Beta)
Manage groups via API
You can also manage groups programmatically using our NerdGraph API. For how to create and manage groups via the API, refer to NerdGraph user management.
Create custom roles (optional)
We have several default-available roles, which we call standard roles. Some of these are assigned to the Admin and User groups that are available by default.
If you have Pro or Enterprise edition, you can create your own custom roles. Creating custom roles is optional. If you don't have a need for custom roles, you can skip this section.
Some tips to help you understand what roles are:
Roles contain the actual permissions. Groups are just containers for users—the roles assigned to those groups determine what users can access.
A role contains various permissions. For example: the permission to create and modify alert conditions, or the permission to delete data ingest license keys (for more information, see Permissions).
To create and manage custom roles:
From the user menu, click Administration > Access Management.
Click the Roles tab.
You'll see the existing standard roles available in your organization.
To create a custom role, click +Add a role.
In the Set role scope step, select your role scope:
- Organization for organization-wide administrative functions
- Accounts for platform features within specific accounts
- Single item or entity for fine-grained access to specific resources
Click Next to proceed to the Role details step and configure based on your selected scope:
Organization-scoped roles:
- Enter a role name.
- Select permissions from organization-level categories (Identity and Access Management, New Relic One, Alerts, Fleet Control, Security, API Keys, Applied Intelligence, Workflow Automation, API Catalog, etc.).
Account-scoped roles:
- Enter a role name.
- Select permissions from platform feature categories (Alerts, APM, Browser, Infrastructure, etc.).
Entity-scoped roles:
- Select the entity type from the dropdown.
- Enter a role name.
- Select permissions specific to that entity type.
Click Save to create the role.
Important
Choose your role scope carefully, as this determines what type of access grants you can create with this role.
Create access grants
Access grants connect your groups to roles over specific targets. You create access grants to give users in a group the permissions defined in a role.
To create access grants:
From the user menu, click Administration > Access Management.
Click the Access Grants tab.
To create a new access grant, click +Create new grant.
Select your authentication domain from the dropdown.
Choose your grant type:
- Organization for organization-scoped roles
- Account for account-scoped roles
- Group for group management roles
Configure the grant components:
Organization grants:
- Select the group that will receive access.
- Select the organization-scoped role.
- Target is automatically your entire organization.
Account grants:
- Select the group that will receive access.
- Select the account-scoped role.
- Select the specific accounts this role applies to.
- Optionally select a data access policy.
Group grants:
- Select the assignee group.
- Select the group-scoped role.
- Select target groups that can be managed.
Click Create grant to save the access grant.
Tip
Group grants allow you to delegate group membership management to non-admin users. The Group Admin role gives users the ability to add and remove users from specified target groups.
Add users
Due to how we bill per calendar month, there are reasons you may want to wait until the beginning of a month to add users. For more on that, see User billing.
If you're using SCIM provisioning, you should be done at this point because your groups and users are imported from your identity provider. You can move to the verification step.
Otherwise, you'll need to add users. In the user management UI, you can see your users and the groups they've been assigned to.
Suggested steps for adding users via the UI:
To view users and see their groups: from the user menu, click Administration, and click User management.
Optional: select your authentication domain using the domain switcher. (Remember that groups reside within the boundaries of an authentication domain).
To add a user, click Add user. Complete the prompts in the UI, including choosing the user type and group. Any custom groups you've added are available from the group dropdown. If the custom group you choose has a role and account assigned, once you add the user to that group, that user will have access.
To edit a user's group or other details: click on the user you want to edit and make changes. For tips on bulk editing and other common tasks, see Common user management tasks.
You can also use our NerdGraph API to add and manage users
Verify things are working
Ideas for checking that your users are configured correctly:
Go to the User management UI and Access management UI and see if the groups and grants assignments look correct and make sense.
Have some of your users see if they can log in and access the accounts they expect to see.
Ideas for next steps:
Add more users