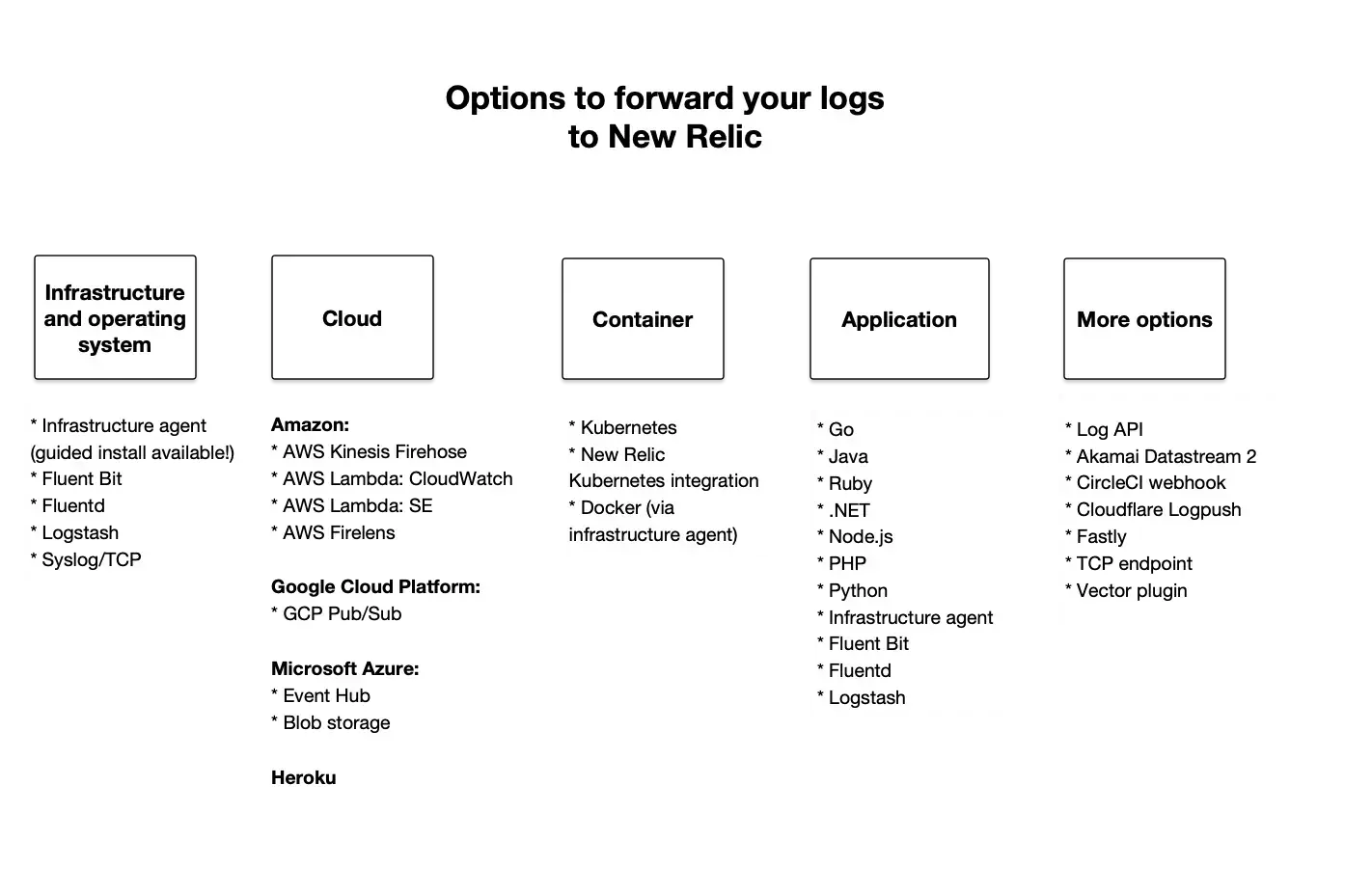
当社の機能は、ログデータの収集、処理、探索、クエリ、およびアラートに役立ちます。ログをNew Relicに取り込むには、次のオプションのいずれかを使用できます。
さまざまなログソリューションの概要については、ログの概要を参照してください。
ヒント
ログがたくさんありますか?それらを最適化および管理する方法については、チュートリアルをご覧ください。
特定の使用例を実現する方法の詳細をいくつか示します。
これを実現したい場合は... | これらのログ転送オプションのいずれかを使用 |
|---|---|
ディスク上のローカルファイルに書き込まれるログを収集する | Infrastructureエージェント( Fluent Bit 、 Fluentd 、 Logstash 、syslog/TCPなど)のソリューションを使用して、 OSからログを転送します。infrastructureモニタリング用のガイド付きインストールを、アプリとホストのログの軽量データコレクターとして使用します。 |
クラウド転送プラットフォームを使用する | クラウドプラットフォーム(Amazon AWS、Google Cloud Platform、Microsoft Azure、Herokuなど)から、サービスレベルログ、アプリケーションログ、インフラストラクチャログ、または上記のすべてを収集します。 |
スタンドアロンまたはKubernetesの使用時に、 Dockerコンテナで実行されているアプリからログを収集する | Kubernetes環境の場合は、Kubernetesプラグインを使用します。 Docker環境の場合、いくつかのオプションが用意されています。
|
ホストされている場所に関係なく、アプリから直接ログを収集する | エージェントとinfrastructureエージェントを使用してください。アプリのAPMエージェントにより、APM logs in contextを使ってログデータをNew Relicに直接転送できるようになります。追加のサードパーティソフトウェアのインストールや保守は必要はありません。 |
その他 | ログ転送オプションがニーズを満たさない場合は、次のことを行えます。
|
ログフォワーダーを使ってみる
ログは、infrastructureエージェントまたはサポートされているサードパーティログサービスのいずれかを介して転送できます。その方法は次のとおりです。
- ログを報告するアカウントのNew Relic を準備します。
- 互換性のあるログフォワーダーをインストールしてください
- TCPポート443でのアウトバウンド接続が、 地域に一致するCIDR範囲に使用できることを確認します
- New Relic内のアカウントデータの保存場所に応じて、設定にはDNS名、
log-api.newrelic.comまたはlog-api.eu.newrelic.comを使用します。 - 該当する場合は、手動のLogs in Context手順に従って、アプリのエージェントを設定します。
ログ転送オプション
APMエージェントの他に、ログをNew Relicに転送するための他のソリューションもいくつか用意しています。
infrastructureエージェント(推奨)とOSソリューション
弊社のinfrastructureエージェントを使用すると、強力なログレポートと設定オプションを提供できるため、ログ管理に推奨される方法の1つです。この設定の詳細については、infrastructureエージェントのログを参照してください。
インフラストラクチャのログ転送に自動的に含まれるホストメトリクスが必要ない場合、または既にログフォワーダーがある場合は、次のオプションのいずれかを使用してログをNew Relicに転送できます。
Amazon
次のAmazonログフォワーダーをサポートしています。
Microsoft
次のMicrosoftログフォワーダーをサポートしています。
サポートされているその他のログフォワーダー
以下のログフォワーダーをサポートしています。これらのオプションの一部には、すぐに使用できるとアラートを提供するクイックスタートが付属しています。ログ転送を設定した後、クイックスタートをインストールできます。
Akamai DataStream 2:
Fastly:
このドキュメントはインストールの役に立ちましたか?
TCPエンドポイント
状況によっては、ログフォワーダーがない場合があります。たとえば、CDN、ハードウェアデバイス、マネージドサービスなどです。rsyslogやsyslog-ngなどのsyslogプロトコルを使用すると、TCPエンドポイントを介してログをNew Relicに転送できます。
ログのAPI
プラグインをインストールせずにNew Relicに接続するには、HTTP入力インテグレーションがあります。このオプションは、Log API経由でモニターログデータをNew Relicに直接送信します。
ログ転送の仕組み
次の図は、エージェントのメタデータによる強化(コンテキストに基づくロギング)から、ログデータのフォーマットとNew Relicへの転送まで、アプリのログメッセージのライフサイクルを示しています。
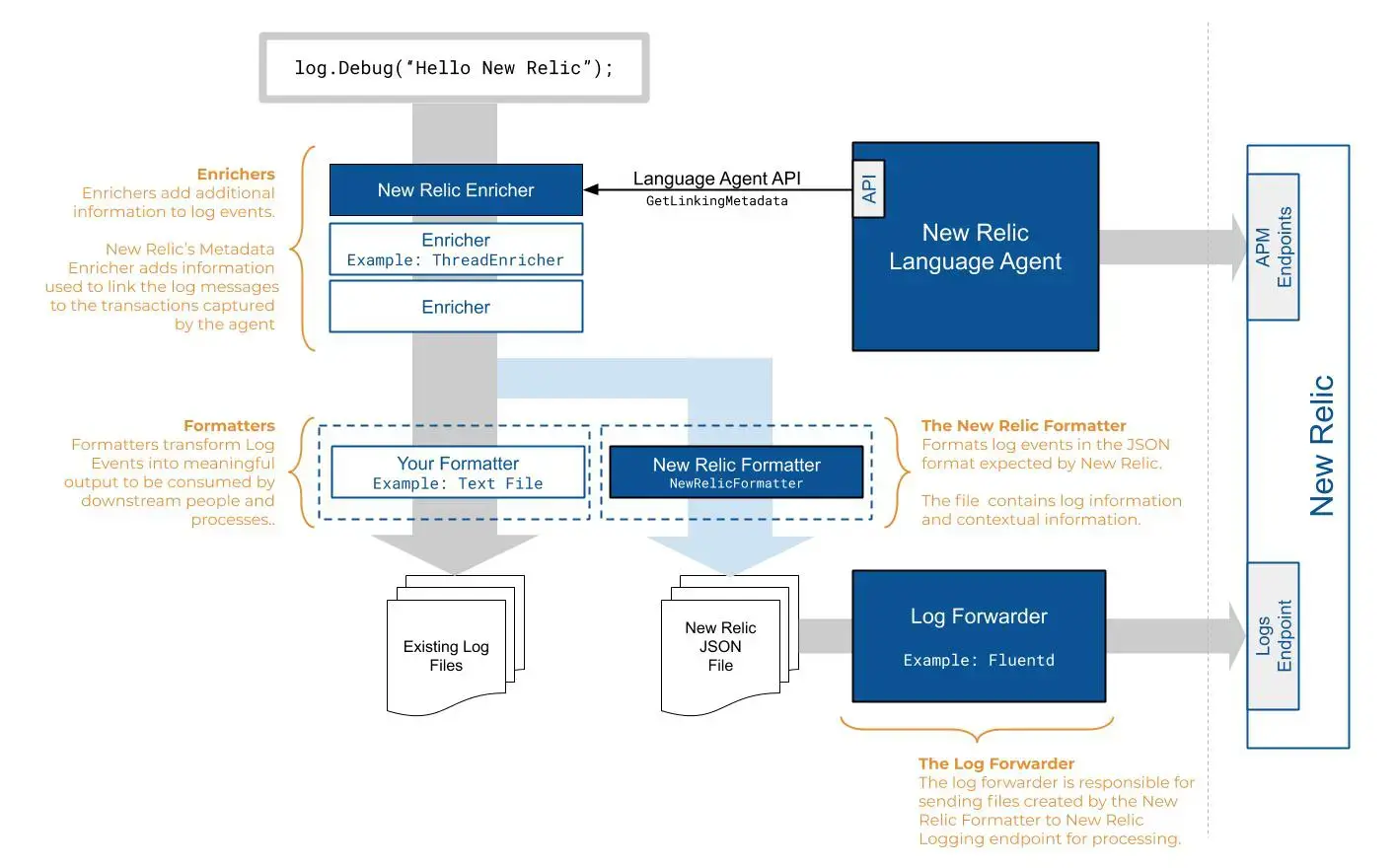
この図は、New Relicを介したログメッセージの流れを示しています。
標準のログフォーマッターは、ログイベントを下流のユーザーやプロセスが使用できる意味のある出力(テキストファイルなど)に変換します。NewRelicFormatterは、ログイベントをNew Relicが期待するJSON形式に変換します。これらのファイルには、ログ情報と拡張メタデータが含まれています。
ログフォワーダー(infrastructureエージェント、Fluentd、Logstashなど)を設定するときに、ログデータを拡張および強化することもできます。Logs in Contextを設定すると、ログエンリッチャーは、フォーマットされたログデータをアプリケーションまたはホストからの追加のトランザクション情報にリンクします。
これで、ログファイルは拡張メタデータとコンテキストに基づくロギングデータで強化されました。ログフォワーダーは、処理のためにファイルをログエンドポイントに送信します。そこからログ管理機能を使用して、New Relicで表示、クエリ、アラートの設定などを行うことができます。
次のステップ
ログフォワーダーを有効にしたら、ログ管理機能を使用してNew Relicのデータを最大限に活用します。
- Logs UIを使用して、プラットフォーム全体のロギングデータを調べます。
- APM UIでアプリのパフォーマンスのコンテキストでログを確認する。ディストリビューティッド(分散)トレーシング、スタックトレース、アプリケーションログなどを使用して、エラーをトラブルシューティングします
- infrastructureエージェントを使用してログを転送すると、アプリケーションとプラットフォームのパフォーマンスデータをより深く可視化することができます。UIでインフラストラクチャログを確認します。
- アラートの設定
- データをクエリし、ダッシュボードを作成します。たとえば、データパーティションルールとログ解析ルールのクエリと管理については、NerdGraphチュートリアルを参照してください