New Relic infrastructure integrations include an integration for AWS Security Lake, allowing you to send your security log data to New Relic.
Collect and send telemetry data to New Relic from Security Lake using our integration. You can use this integration to monitor your services, query incoming data, and build dashboards to observe everything at a glance.
Activate integration To enable this integration, set up an S3 log forwarder. We suggest using our serverless forwarder application for ease and convenience, but you can also set your own.
Tip You have two options for Security Lake monitoring setup. You can consolidate multiple regions to avoid repeating steps, or you can set it up on a per-region basis.
For more details, see managing multiple regions .
Prerequisites Before enabling this integration, first make sure these steps are completed for Security Lake:
Complete the steps mentioned in the Amazon Security Lake Getting started guide . Complete the prerequisites to setting up a subscriber with data access by following the steps in the Security Lake subscriber guide . Configuration steps Here's an overview of the steps you'll be doing:
Create a Security Lake subscriber .Install our dedicated Amazon Security Lake log forwarder .Find and use your log data .Create a Security Lake subscriber Navigate to the Security Lake feature in your AWS Console .
Select Subscribers , and select Create Subscriber .
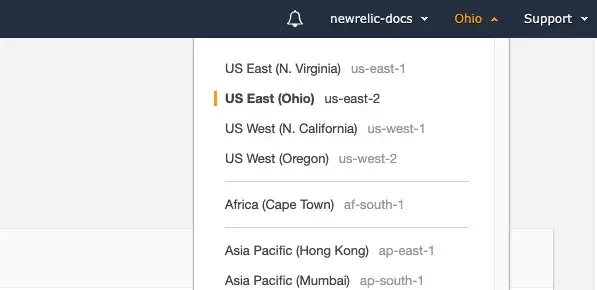
Give the subscriber a name and select a region.
Select which log and event sources you want sent to New Relic.
Fill out the remaining details as described below:
Field
Value
Data access method
S3
Account ID
Insert the AWS account ID where you plan on installing the New Relic-provided serverless application.
External ID
Insert your New Relic AccountID. For more info, see externalID
Notification details
SQS queue
Select Create .
From the Subscriber details page, copy your AWS role ID and Subscription endpoint ARN's. You will need them for the next step.
Install our Amazon Security Lake log forwarder To install the log forwarder:
Open the AWS Serverless Application Repository in your browser.
Search for newrelic and check Show apps that create custom IAM roles or resource policies to find the newrelic-securitylake-s3-processor-LogForwarder. Click the newrelic-securitylake-s3-processor-LogForwarder details, and click Deploy . Copy/paste the AWS role ID ARN from the previous step into the SecurityLakeSubscriberRoleArn field. Copy/paste the Subscription endpoint ARN from the previous step into the SecurityLakeSubscriberRoleArn field. Input the ExternalID that you added in the previous step. Input your license key into the NRLicenseKey field. Acknowledge and select Deploy . For more details on this, see our Amazon Security Lake log forwarder docs .
Find and use Log data To find your logs on New Relic, go to one.newrelic.com > All capabilities > LogsAttributes to product.name, and then choose the log source you want.
The following log sources are currently supported:
Tip Amazon Security Lake uses the OCSF Schema for its logs.
Here are attributes you can find in Security Lake logs:
VPC Flow Logs Query Amazon VPC logs to view data for the following attributes:
Name
Description
Data type
activity_id
activity ID
integer
activity_name
activity name
string
aws.invoked_function_arn
ARN of the invoked log forward function
string
aws.s3_bucket_name
name of the S3 bucket where the log was forwarded from
string
aws.s3_key
key record of the security event from the flow log
string
category_name
name of the category of the log
string
category_uid
unique ID of the category
integer
class_name
name of the log class
string
class_uid
unique ID of the class
integer
cloud.account_uid
AWS account where the flow log originated
string
cloud.provider
shows the name of the cloud provider - in this case AWS
string
cloud.region
AWS region where the flow log originated
string
cloud.zone
AWS zone where the flow log originated
string
connection_info.boundary
boundary of the flow log
string
connection_info.boundary_id
ID of the boundary
integer
connection_info.direction
shows if the connection was inbound or outbound
string
connection_info.direction_id
ID of the direction
integer
connection_info.protocol_num
protocol number of the flow
integer
connection_info.protocol_ver
protocol version
string
connection_info.tcp_flags
TCP flags
integer
dst_endpoint.instance_uid
instance ID of the destination
string
dst_endpoint.interface_uid
interface ID of the destination
string
dst_endpoint.intermediate_ips
intermediate IP addresses of the destination
string
dst_endpoint.ip
IP address of the destination
string
dst_endpoint.port
port of the destination
integer
dst_endpoint.subnet_uid
subnet ID of the destination
string
dst_endpoint.svc_name
service name of the destination
string
dst_endpoint.vpc_uid
VPC ID of the destination
string
end_time
end time of the flow
integer
logtype
defines the logtype
string
metadata.product.feature.name
name of the feature where the log originated
string
metadata.product.name
name of the product where the log originated
string
metadata.product.vendor_name
name of the vendor for the log; in this case AWS
string
metadata.product.version
name of the product version
string
metadata.profiles
names of the profiles
string
metadata.version
metadata version
string
newrelic.source
source of the log in New Relic
string
plugin.type
type of plugin used
string
plugin.version
version of plugin used
string
severity
severity level of the log finding
string
severity_id
ID of the severity level
integer
src_endpoint.instance_uid
instance ID of the source
string
src_endpoint.interface_uid
interface ID of the source
string
src_endpoint.intermediate_ips
intermediate IP addresses of the source
string
src_endpoint.ip
IP address of the source
string
src_endpoint.port
port of the source
integer
src_endpoint.subnet_uid
subnet ID of the source
string
src_endpoint.svc_name
service name of the source
string
src_endpoint.vpc_uid
VPC ID of the source
string
start_time
start time
integer
time
start time
integer
timestamp
time of the log reaching New Relic
integer
traffic.bytes
amount of bytes being sent or received
integer
traffic.packets
amount of packets being sent or received
integer
type_name
event type name
string
type_uid
ID of the event type
integer
unmapped
unparsed data not mapped to a field
string
CloudTrail Query CloudTrail logs to view data for the following attributes:
Name
Description
Data type
activity_id
activity ID
integer
activity_name
activity name
string
api.operation
operation of the API activity
string
api.request.uid
unique ID of the API request
string
api.response.error
error response of the API request
string
api.response.message
message of the API response
string
api.service.name
name of the service where the request originated
string
api.version
API version
string
aws.invoked_function_arn
ARN of the invoked log forward function
string
aws.s3_bucket_name
name of the S3 bucket where the log was forwarded from
string
aws.s3_key
key record of the security event from the flow log
string
category_name
name of the category of the log
string
category_uid
unique ID of the category
integer
class_name
name of the log class
string
class_uid
unique ID of the class
integer
cloud.provider
shows the name of the cloud provider - in this case AWS
string
cloud.region
AWS region where the flow log originated
string
http_request.user_agent
user agent of the HTTP request
string
identity.idp.name
IDP name of the requester
string
identity.invoked_by
name of the feature invoking the request
string
identity.session.created_time
session creation time
integer
identity.session.issuer
ARN of the issuer
string
identity.session.mfa
MFA enabled
boolean
identity.user.account_uid
AWS account of the user
string
identity.user.credential_uid
credential ID of the user
string
identity.user.name
name of the user
string
identity.user.type
type of user
string
identity.user.uid
ID of the user
string
identity.user.uuid
ARN of the user
string
logtype
defines the logtype
string
metadata.product.feature.name
name of the feature where the log originated
string
metadata.product.name
name of the product where the log originated
string
metadata.product.vendor_name
name of the vendor for the log; in this case AWS
string
metadata.product.version
name of the product version
string
metadata.profiles
names of the profiles
string
metadata.version
metadata version
string
newrelic.source
source of the log in New Relic
string
plugin.type
type of plugin used
string
plugin.version
version of plugin used
string
ref_event_uid
unique ID for reference event
string
resources
resources
string
severity
severity level of the log finding
string
severity_id
ID of the severity level
integer
src_endpoint.domain
domain of the source
string
src_endpoint.ip
IP address of the source
string
src_endpoint.uid
unique ID of the source
string
time
start time
integer
timestamp
time of the log reaching New Relic
integer
type_name
event type name
string
type_uid
ID of the event type
integer
unmapped
unparsed data not mapped to a field
string
Security Hub Logs Query Security Hub logs to view data for the following attributes:
Name
Description
Data type
activity_id
activity ID
integer
activity_name
activity name
string
answers
answers
string
aws.invoked_function_arn
ARN of the invoked log forward function
string
aws.s3_bucket_name
name of the S3 bucket where the log was forwarded from
string
aws.s3_key
key record of the security event from the flow log
string
category_name
name of the category of the log
string
category_uid
unique ID of the category
integer
class_name
name of the log class
string
class_uid
unique ID of the class
integer
cloud.account_uid
ID of the AWS account
string
cloud.provider
shows the name of the cloud provider - in this case AWS
string
cloud.region
AWS region where the flow log originated
string
connection_info.direction
direction of the connection
string
connection_info.direction_id
ID for the direction of the connection
integer
connection_info.protocol_name
protocol of the connection
string
dst_endpoint.instance_uid
destination instance ID
string
dst_endpoint.interface_uid
destination interface ID
string
logtype
defines the logtype
string
metadata.product.feature.name
name of the feature where the log originated
string
metadata.product.name
name of the product where the log originated
string
metadata.product.vendor_name
name of the vendor for the log; in this case AWS
string
metadata.product.version
name of the product version
string
metadata.profiles
names of the profiles
string
metadata.version
metadata version
string
newrelic.source
source of the log in New Relic
string
plugin.type
type of plugin used
string
plugin.version
version of plugin used
string
query.class
query class
string
query.hostname
query hostname
string
query.type
query type
string
rcode
response code
string
rcode
response code ID
integer
severity
severity level of the log finding
string
severity_id
ID of the severity level
integer
src_endpoint.instance_uid
instance ID of the source
string
src_endpoint.ip
IP address of the source
string
src_endpoint.port
port of the source
integer
src_endpoint.vpc_uid
VPC ID of the source
string
time
start time
integer
timestamp
time of the log reaching New Relic
integer
type_name
event type name
string
type_uid
ID of the event type
integer
unmapped
unparsed data not mapped to a field
string
Route 53 Resolver Query Logs Query Route 53 logs to view data for the following attributes:
Name
Description
Data type
activity_id
activity ID
integer
activity_name
activity name
string
aws.invoked_function_arn
ARN of the invoked log forward function
string
aws.s3_bucket_name
name of the S3 bucket where the log was forwarded from
string
aws.s3_key
key record of the security event from the flow log
string
category_name
name of the category of the log
string
category_uid
unique ID of the category
integer
class_name
name of the log class
string
class_uid
unique ID of the class
integer
cloud.account_uid
ID of the AWS account
string
cloud.provider
shows the name of the cloud provider - in this case AWS
string
cloud.region
AWS region where the flow log originated
string
compliance.requirements
compliance requirements
string
compliance.status
compliance status
string
compliance.status_detail
details about the compliance status
string
confidence
confidence
string
finding.created_time
creation time of the finding
integer
finding.desc
description of the finding
string
finding.first_seen_time
time when the finding was first seen
integer
finding.last_seen_time
time when the finding was last seen
integer
finding.first_seen_time
time when the finding was first seen
string
finding.modified_time
time when the finding was modified
integer
finding.related_events
events related to the finding
string
finding.remediation.desc
information about the remediation for the finding
string
finding.remediation.kb_articles
knowledge base articles about the remediation for the findings
string
finding.src_url
URL for the source of the finding
string
finding.title
title of the finding
string
finding.types
list of types relative to the finding
string
finding.uid
ARN of the finding
string
logtype
defines the logtype
string
malware
malware
string
metadata.product.feature.name
name of the feature where the log originated
string
metadata.product.name
name of the product where the log originated
string
metadata.product.vendor_name
name of the vendor for the log; in this case AWS
string
metadata.product.version
name of the product version
string
metadata.profiles
names of the profiles
string
metadata.version
metadata version
string
newrelic.source
source of the log in New Relic
string
plugin.type
type of plugin used
string
plugin.version
version of plugin used
string
process.created_time
process creation time
string
process.file.name
process file name
string
process.file.path
process file path
string
process.file.type_id
process file type ID
integer
process.name
process name
string
process.parent_process.pid
process ID of the parent process
string
process.pid
process ID
string
process.terminated_time
process termination time
string
resources
resources
string
severity
severity level of the log finding
string
severity_id
ID of the severity level
integer
state
state of the finding
string
state_id
state ID of the finding
string
time
start time
integer
timestamp
time of the log reaching New Relic
integer
type_name
event type name
string
type_uid
ID of the event type
integer
unmapped
unparsed data not mapped to a field
string
vulnerabilities
vulnerabilities
string
How to use your data To know more about how to use your data, see understand integration data .
Alerts You can set up alerts to notify you of breaking changes. For example, an alert can be set up to notify relevant parties of critical or fatal errors.
Learn more about creating alerts .
Other AWS integrations Read more about New Relic AWS integrations: