自動化されたユーザー管理 、IDプロバイダー(OneLoginやOktaなど)のユーザーやグループは、New Relicと同期されます。
グループの仕組み
自動ユーザー管理を使用する場合、ID プロバイダー サービスでユーザーのグループを作成します。後で、New Relic 側で、 ロールとアカウントへのグループ アクセスを割り当てます。
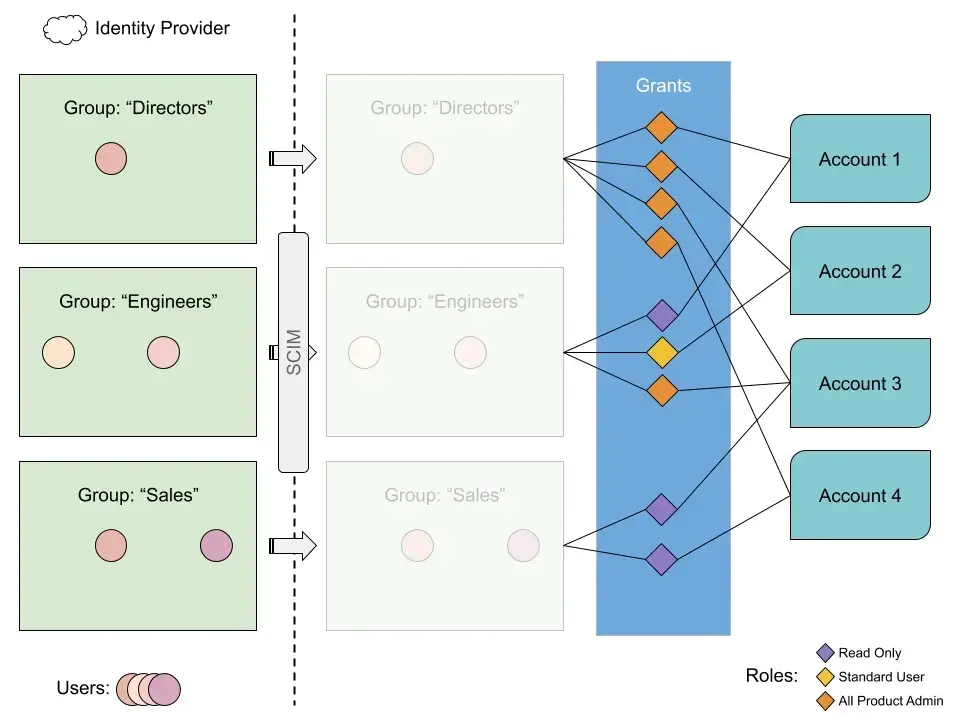
ID プロバイダーのユーザー グループが New Relic グループ アクセス (1 つ以上のアカウントの特定のロールにアクセスできるグループ) にマップされる方法の例。
上記の例では、エンジニア グループに注目してみましょう。 SCIM を介して、New Relic は 2 つのユーザー レコードと、それらがエンジニア グループに属しているという情報を受け取ります。 この例では、設定は次のようになります: 2 人のエンジニア ユーザーは、アカウント 1 でRead onlyロール、アカウント 2 でStandard userロール、アカウント 3 でAll product adminロールを持ちます。
このアクセスは、New Relic のEngineersグループにいくつかのロールとアカウントを割り当てることによって許可されます。
アカウント 1 のグループ
Engineers
にロール
Read only
割り当てます
アカウント2のグループ
Engineers
にロール
Standard user
割り当てます
アカウント3のグループ
Engineers
にロール
All product admin
を割り当てます
ユーザー アクセスの仕組みの詳細については、「 ユーザー管理の概念」を参照してください。
新しいグループやカスタムロールの作成についてのチュートリアルは、 ユーザー管理のチュートリアル をご覧ください。