New Relicユーザーを設定して管理するには、まずユーザー管理システムの仕組みに関する基本的な概念を理解する必要があります。
ユーザーアクセスの概要
ユーザーが製品機能にアクセスできるかどうかは、次の2つの要素によって制御されます。
- ユーザータイプ(ベーシックユーザー、コアユーザー、フルプラットフォームユーザー):ユーザーのユーザータイプは、対象ユーザーがNew Relicをどの程度使用すると予想されるかに基づきます。ユーザータイプは課金要素です。これは権限を設定するためのものではありません。詳細については、ユーザータイプを参照してください
- ロールベースのアクセス:これは、ロール(権限のセット)、グループ(ユーザーのコンテナ)、アクセス許可(特定のターゲットに対するグループとロール間のリンク)を通じてユーザーの権限を制御するために使用するものです。
これらは2つの個別のシステムです。New Relicの機能にアクセスできるようにするには、ユーザータイプとロールベースの権限の両方でそのアクセスが許可されている必要があります。ユーザーのタイプとロールの関係について詳しくは、ユーザータイプとロールを参照してください。このドキュメントでは、ロールベースのアクセスに焦点を当てています。
ロールベースのアクセスに加えて、データアクセス制御を使用して、特定のログデータへのアクセスを制御することもできます。これにより、ユーザーが表示できるログパーティションを制限できます。
グループ、ロール、アクセス権限によるNew Relicへのアクセス制御
New Relicでは、ユーザーgroupsにはユーザーが含まれ、 rolesにはpermissionsが含まれています。アクセス権限は、特定のターゲット上のロールにグループを明示的にリンクするaccess grantsを通じて付与されます。New RelicユーザーがNew Relic機能にアクセスするには、次のアクセス権限を持つグループにユーザーを配置する必要があります。
ProまたはEnterpriseエディションを使用する組織は、組織内に複数のアカウントを持つことができ、カスタムロールとグループを作成できます。カスタムロールは、管理機能の組織レベル、プラットフォーム機能のアカウントレベル、特定のリソースへのきめ細かなアクセスのエンティティレベルの3つの異なるスコープで作成できます。FreeエディションとStandardエディションでは、組織内で1つのアカウントのみ許可され、カスタムロールやグループを作成することができません。
New Relicに初めてサインアップすると、組織には、デフォルトのUserまたはAdminグループ向けに事前定義済みのロールとアカウントが複数用意されています。たとえば、 Adminグループには、上位レベルの管理権限や組織規模の機能管理といった広範なNew Relicアクセスをグループ内のユーザーに付与するロールが複数用意されています。
ヒント
ユーザーがNew Relicにアクセスする方法を制御する場合は、こちらで認証ドメインを管理します。
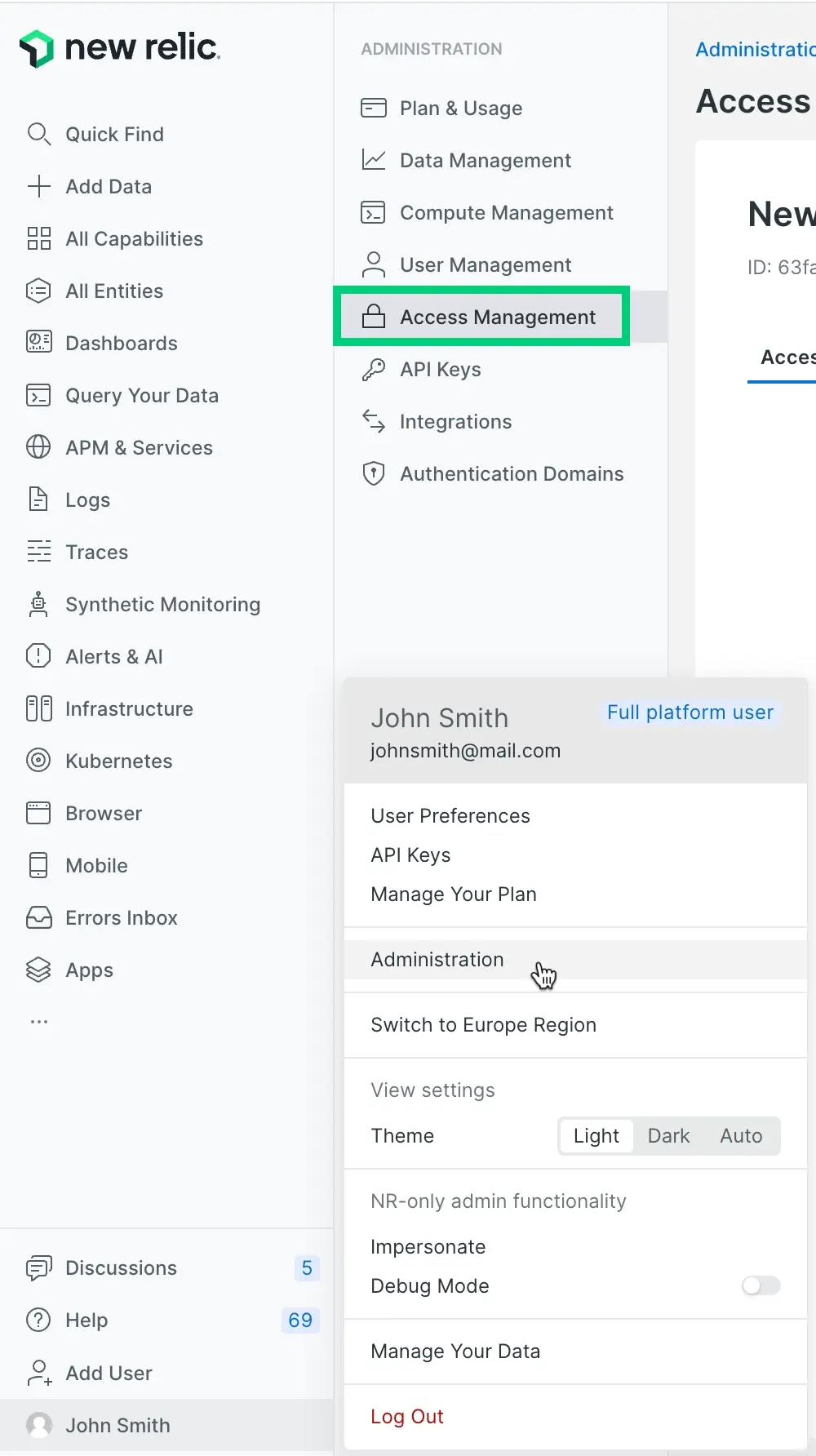
Access management UIのビュー。デフォルトのグループ(AdminとUser )に、ロール、アカウント、組織スコープの権限へのアクセス権がどのように付与されるかを表示します。
以下は、グループアクセスがどのように機能するか、また、より大規模な組織にどのように関連しているかを示す図です。
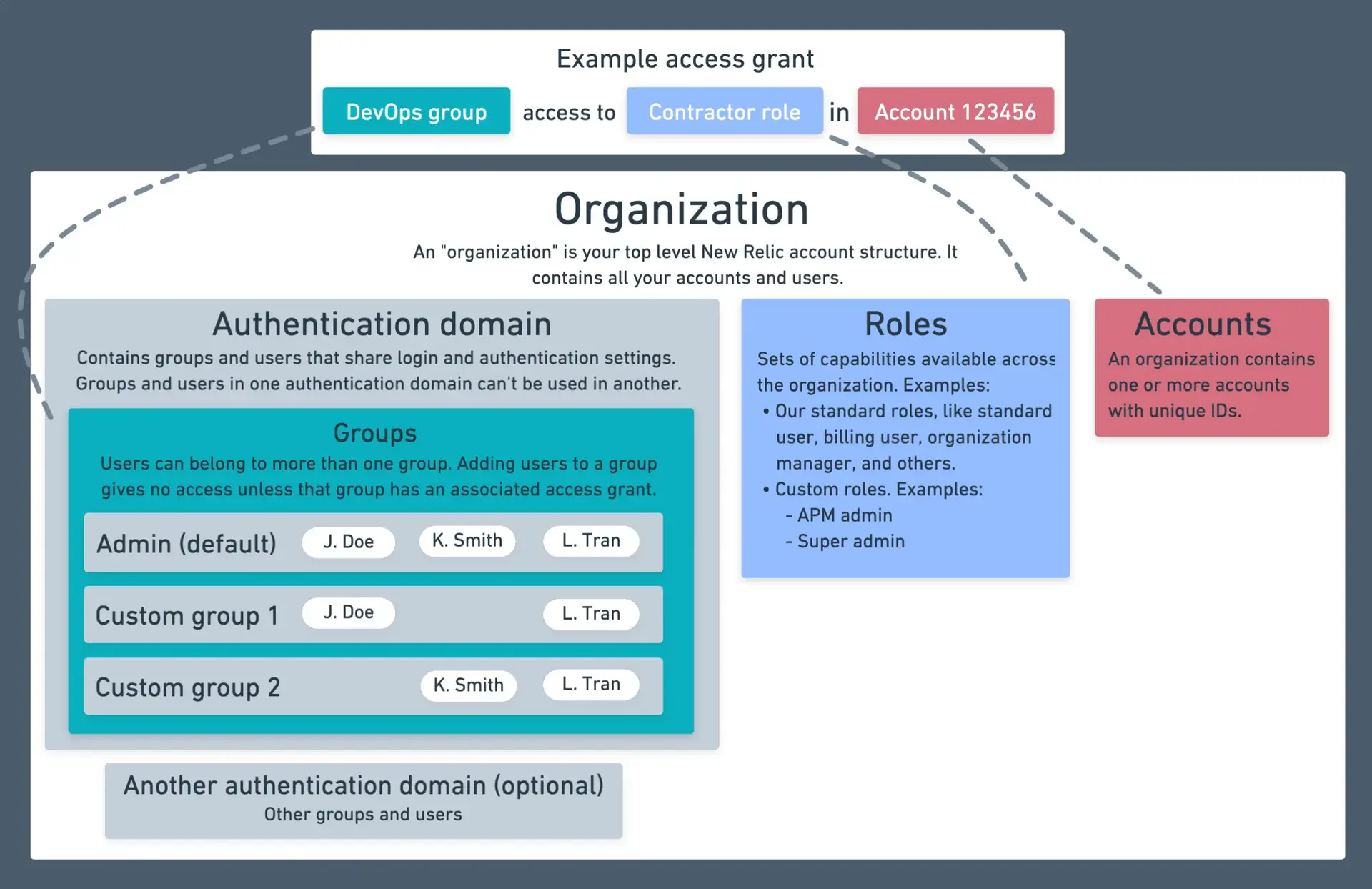
グループが、そのグループのユーザーにロールとアカウントへのアクセス権を付与する方法を示す図。
グループの設定に関するヒントについては、ユーザー管理チュートリアルを参照してください。
アクセス権限
Access grants 特定のターゲット上のロールにグループを接続する明示的なリンクです。アクセス権限を作成して、特定のスコープに対して適用される、ロールで定義された権限をグループ内のユーザーに付与します。
すべてのアクセス権限には、次の3つのコンポーネントが必要です。
- 担当者:アクセスを受け取るグループ
- ロール:付与される権限のセット
- ターゲット:ロールが適用されるリソースのスコープ
スコープに基づいて、次の3種類のアクセス権限を作成できます。
組織権限
組織権限を適用して、グループに組織レベルの権限を付与します。これらの権限には、以下の機能があります。
- 組織全体をターゲットにします。
- 組織スコープのロールが必要です。
- 組織全体の機能に対する権限をユーザーに付与します。
アカウント権限
アカウント権限を適用して、特定のアカウント内のプラットフォーム機能へのアクセス権をグループに付与します。これらの権限には、以下の機能があります。
- アカウントスコープのロールが必要です。
- グループがアクセスできるアカウントを選択できます。
- ログデータの可視性を制御するためのデータアクセスポリシーを含めることができます。
グループ権限
グループ管理の責任を委任するには、グループ権限を適用します。これらの権限には、以下の機能があります。
- グループスコープのロール(グループ管理者など)が必要です。
- 担当者グループが管理できるグループを指定できます。
- 広範な管理アクセスなしで分散ユーザー管理を有効にします。
アクセス権限を作成する手順については、ユーザー管理チュートリアルを参照してください。
グループ
New Relicで、ユーザーをgroupに配置すると、複数のユーザーを同時に管理できます。 たとえば、自動ユーザー管理機能を使用している場合は、IDプロバイダーサービスからユーザーのカスタムグループ(たとえば、External consultants ) をインポートし、そのグループにロールとアカウントを付与できます。
New Relicの機能にアクセスするには、ユーザーがロールと1つ以上のアカウントにアクセスできる、1つ以上のグループに属している必要があります。 グループはユーザーのNew Relic権限を制限するものではありません。グループに割り当てられたroleで、権限へのアクセスを許可します。
デフォルトでは、2つのシンプルなユーザーグループを使用できます。また、ProおよびEnterpriseの組織は、カスタムグループを作成できます。ユーザーとグループは、認証ドメイン内にあります。ここで、ユーザーのプロビジョニング方法(IDプロバイダー経由など)と、ユーザーのログイン方法に関連する設定を制御します。
デフォルトのユーザーグループ
2つのデフォルトのユーザーグループがあります。
- User:このグループのユーザーはオブザーバビリティおよびモニタリングの使用と設定ができますが、請求の管理や他のユーザーの管理などのアカウントレベルのタスクを実行することはできません。すべてのオブザーバビリティプラットフォームツールの制御を許可するAll product adminロールと、製品管理権限を持つ組織スコープのロールにアクセスできます。ユーザー管理機能を備えた組織スコープのロールにはアクセスできません。
- Admin:All product adminロールがあり、さらに組織レベルの利用可能なすべての権限を持つ組織スコープのロールにアクセスできます。その結果、このグループは、より高いレベルの管理者機能を含むすべての機能にアクセスできます。
ユーザーが所属するグループを編集するには、 Access management UI に移動してグループを編集するか、 User management UI に移動してユーザーを編集します。
ロール
デフォルトのロールをいくつか用意していますが、プロまたはエンタープライズエディションの組織は、3つのロールスコープのいずれかで独自のカスタムロールを作成できます。
ロールスコープ
それぞれ異なる目的を果たす3つの異なるスコープでロールを作成できます。
組織スコープのロール:これらのロールは、認証ドメインの管理、アカウントの作成、組織設定の構成、スコアカードとチームの管理などの組織全体の機能に適用します。標準ロールに含まれるもの:
- Organization manager: アカウントの追加、組織とアカウントの名前の変更など、組織の設定に関連する権限。これには、特定のエンティティの削除など、機密性の高い監視タスクも含まれます。
- Authentication domain manager: 認証ドメインの構成やグループとロールのカスタマイズなど、ユーザーの追加と管理に関連する権限。
- Billing:ユーザーは請求と使用状況、データ保持期間を表示および管理できます。複数のアカウントを持つ組織の場合、請求はreporting account (通常は組織で最初に作成されたアカウント)に集約されます。
- Organization product admin:スコアカードやチーム管理など、組織スコープのオブザーバビリティ機能に関連する権限。これは組織スコープの全製品管理者に相当します。
Organization read only:New Relicプラットフォームにおける組織スコープの機能への読み取り専用アクセスを提供します。
アカウントスコープのロール:これらのロールを適用すると、APM設定の構成、アラートの管理、クエリの実行など、特定のアカウント内のプラットフォーム機能にアクセスできます。これらは、ほとんどのユーザーが使用する従来のロールです。標準ロールに含まれるもの:
- All product admin: 組織レベルの設定、ユーザー、請求を管理する機能を除く、すべてのNew Relicプラットフォーム権限が含まれています。
- Standard user: 当社のプラットフォーム機能へのアクセスを提供しますが、これらの機能を設定するための権限がなく、組織レベルおよびユーザー管理の権限がありません。
- Read only:New Relicプラットフォームにおけるアカウントスコープの機能への読み取り専用アクセスを提供します。
エンティティスコープのロール:ロールを適用すると、個々のフリートやアラートポリシーなど各リソースへのアクセスをきめ細かく制御できます。これにより、個々のリソースレベルで正確な権限制御が可能になります。ニーズに応じて、カスタムのエンティティスコープロールを作成できます。
ロールに関する重要なポイント:
- 追加的なロール:複数のロールが割り当てられているユーザーは、それらのロールによって付与されたすべての権限があります。たとえば、アカウントで
All product adminのロールを付与するグループと、同じアカウントでRead onlyのロールを付与する別のグループに属している場合は、両方のロールがあり、Read onlyのロールによって制限されません。 - アクセスは、ユーザータイプと権限の両方によって異なります(詳細はこちら)。
- ロールを作成しても、グループをそのロールにリンクするアクセス権限を作成するまでアクセスは許可されません。
ロールおよび権限を表示するには、 Access management UIに移動し、 Rolesをクリックします。
標準(デフォルト)ロール
アカウントスコープのstandard rolesがいくつかあります。これらのロールはデフォルトで利用でき、一般的なユーザー管理のユースケースを満たしています。
重要
標準ロールの一部には、公開されていない権限があるため、カスタムロールへの追加はできないことに留意してください。カスタムロールで複製できる唯一の標準ロールは、Standard userとRead onlyで、その他のすべてには非公開の権限があります。
これは、当社の標準ロールの表です。これらのロールをさらに理解するには、アクセス管理UIに移動してロールを選択します。
標準ロール | 説明 | ユーザータイプのガイドライン |
|---|---|---|
All product admin | このロールには、組織レベルの設定、ユーザー、請求を管理する機能をexcept、すべてのNew Relicプラットフォーム権限が含まれています。これは、プラットフォーム機能(設定を構成する機能など)の設定を許可するという意味で管理者ロールですが、組織レベルの管理者権限(管理者設定を要する権限)は提供しません。 このロールは、基本的には下記のStandard userロールに加えて、オブザーバビリティ機能を設定する機能が追加されています。 | 任意。推奨:コアまたはフルプラットフォーム。 |
Standard user | 当社のプラットフォーム機能(APM UIやUIなど)へのアクセスを提供しますが、これらの機能を設定するための権限や、組織レベルおよびユーザー管理の権限はありません。 アクセス管理UIを使用して、プラットフォーム全体の標準ユーザーロールに含まれる機能を表示します。 | 任意。推奨:コアまたはフルプラットフォーム。 |
Read only | New Relicプラットフォームへの読み取り専用アクセスを提供します(合成モニターのセキュア資格情報を除く)。 | 任意。 |
ロールをグループに割り当てる方法およびカスタムロールを作成する方法の詳細については、ユーザー管理チュートリアルを参照してください。
組織レベルの権限
組織スコープのカスタムロールを作成すると、IDとアクセスの管理、組織の設定、組織の製品管理など、さまざまな組織レベルの権限を割り当てることができます。フルプラットフォーム管理者は、組織の特定のニーズに基づいて、これらの権限をカスタムロールに組み合わせることができます。ベーシックユーザーはこれらの権限を持つロールを使用できません。
グループ管理者
グループにGroup adminロールを割り当てることができます。このロールにより、選択した 1 つ以上のターゲットグループに対してユーザーを追加および削除する権限がグループに付与されます。
これは、完全なユーザー管理権限を持つ、より強力なAuthentication domain managerロールをユーザーに付与するよりも望ましい場合があります。たとえば、会社内に組織全体のユーザー管理権限を持つ管理者が1人か2人しかいない場合でも、さらに数人の管理者に特定のチームのユーザーを管理する権限を与えたい場合があります。
Group adminロールを使用するには、 group access grantを作成し、ロールをグループに割り当て、管理できるターゲットグループを割り当てます。
アクセス権限
ロールが持つ権限およびカスタムロールに追加できる権限については、権限を参照してください。
ユーザーの管理
ユーザーを追加する方法、グループに割り当てる方法、カスタムグループおよびロールを作成する方法については、ユーザーの管理を参照してください。
APIの使用
API経由でユーザー、グループ、ロールを管理する方法については、NerdGraphドキュメントを参照してください。
ユーザー管理の用語と定義
アカウントおよびロールへのユーザーアクセスの仕組みについては、ユーザー管理の概念を参照してください。ここでは、ユーザー管理用語の定義をいくつかご紹介します。
- New Relicのorganizationは、アカウント、ユーザー、データをすべて含む組織を表すものです。詳細については、 組織とアカウント構造を参照してください。
- permissionは、特定のきめ細かなNew Relic機能を使用または編集する機能です。詳細については、 権限を参照してください。
- roleは一連の権限です。これはユーザーに権限を与えるものです。デフォルトの標準ロールにはさまざまな権限があり、カスタム権限を持つカスタムロールを作成できます。
- ユーザーgroupには、1つ以上のロールが関連付けられています。 ユーザーをグループに割り当てます。 デフォルトのユーザーグループ(AdminとUser )があり、独自のグループも作成できます。
- authentication domainには、New Relicに追加され、同じ方法でNew Relic にログインする一連のユーザーが含まれます。
- ユーザーがベーシックユーザーの場合、これはロール関連の権限よりも優先されます。詳細については、ベーシックユーザーとロールを参照してください。