モニター対象の各システムについて、これらの設定タスクを完了してください。
アップロード承認ロール
SAP transaction
PFCGを使用します。Role > Upload に移動し、インストレーション パッケージからファイル_NEWR_DATA_PROVIDER.SAPをアップロードします。
ロール
/NEWR/DATA_PROVIDERがロードされることを確認します。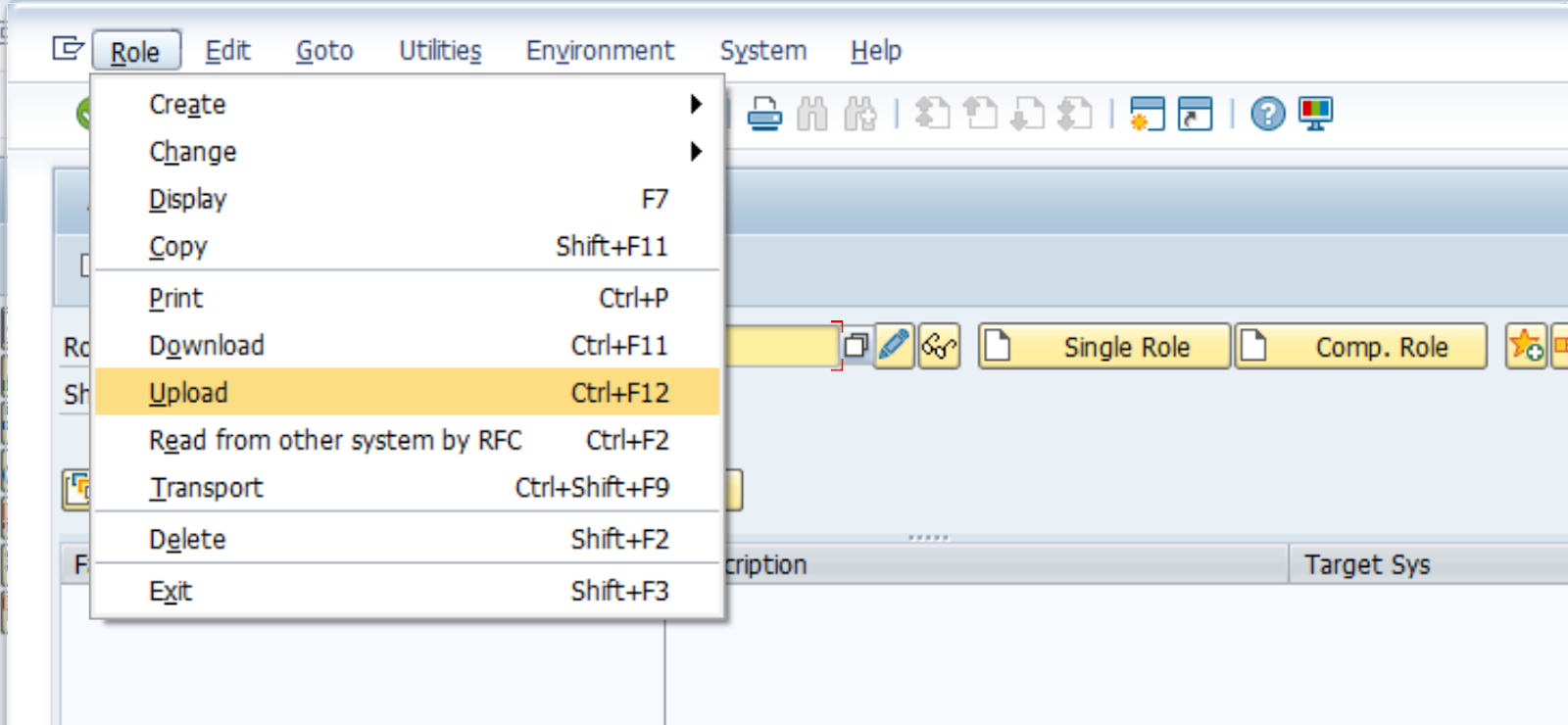

ロールがロードされた後のアイコン。
Authorizationsタブで、

Change Authorization Data、次を使用して有効化します
 アイコン。
アイコン。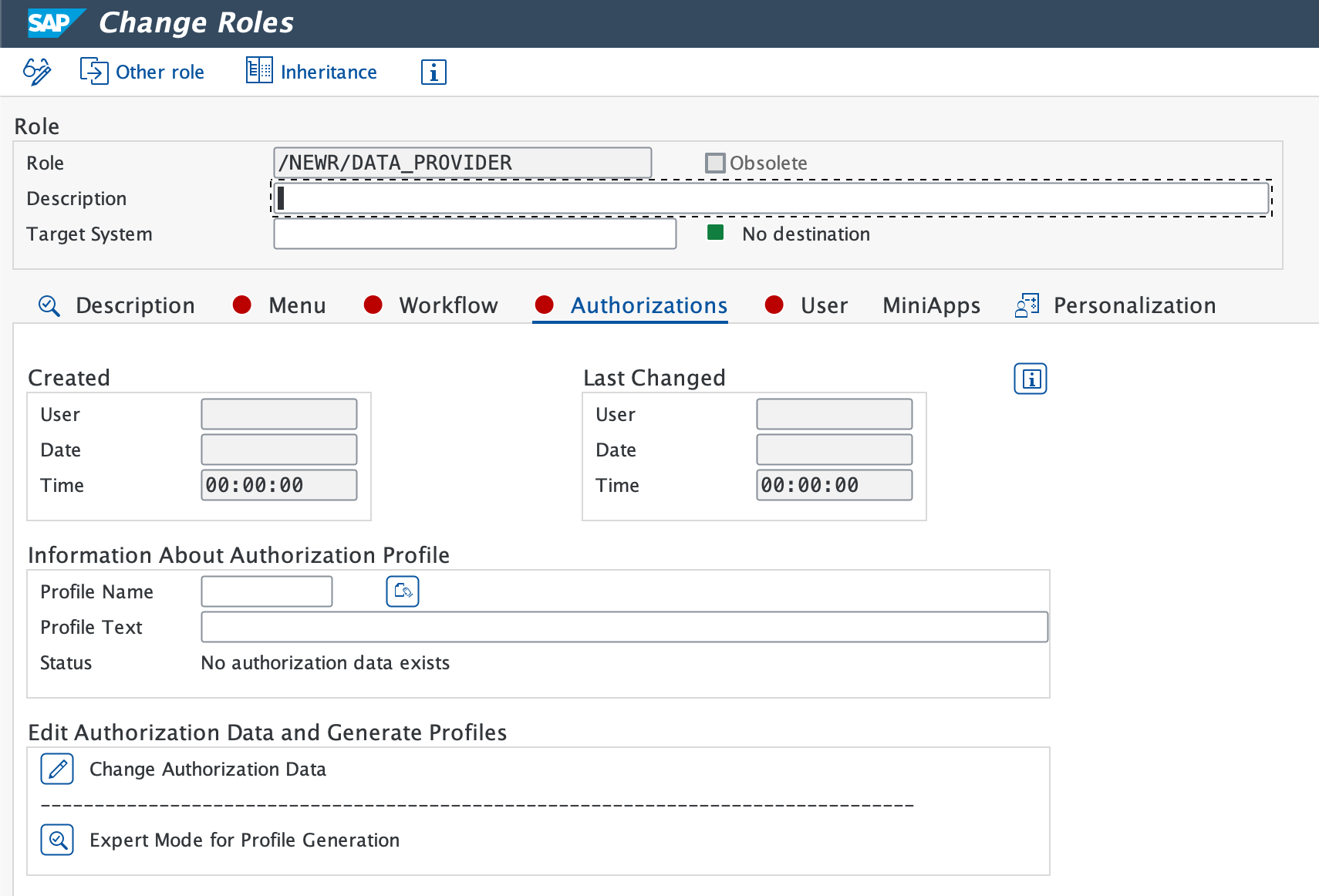
プロファイル名が提案された場合は、緑色のチェックアイコンを選択します。
ステータス バーにProfile(s) were updatedが表示されていることを確認します。
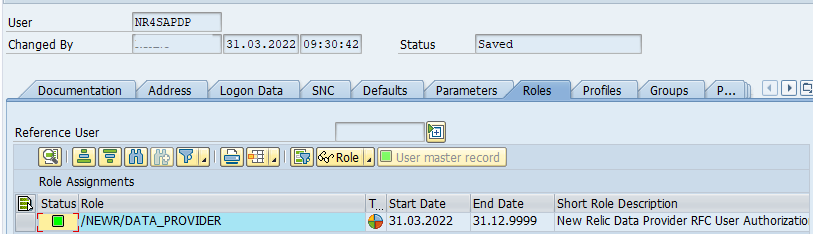
New Relic RFC ユーザー ID の作成
authorization profileをアクティブ化した後、トランザクションSU01を使用して新しいRFC user ID(例:NR4SAPDP)を作成します。user typeをSystemまたはCommunicationに設定し、ロール/NEWR/DATA_PROVIDERを追加します。
監視システムの RFC 宛先を作成する
モニターシステムごとにトランザクションSM59を使用して、RFC destinationを作成します。
ABAP Connectionsを選択し、次にCreateアイコンを選択して新しいRFC destinationを設定します。
分かりやすいRFC Destination名を入力します。以下をお勧めします:
NR_<SYSID>CLNT<CLNT#>Connection Typeを
3 - ABAP Connectionに設定します。Technical Settingsタブで、次を入力します。
- Target Host (完全修飾ドメインまたは IP)と Instance No.
- Gateway Host 、必要に応じてService。
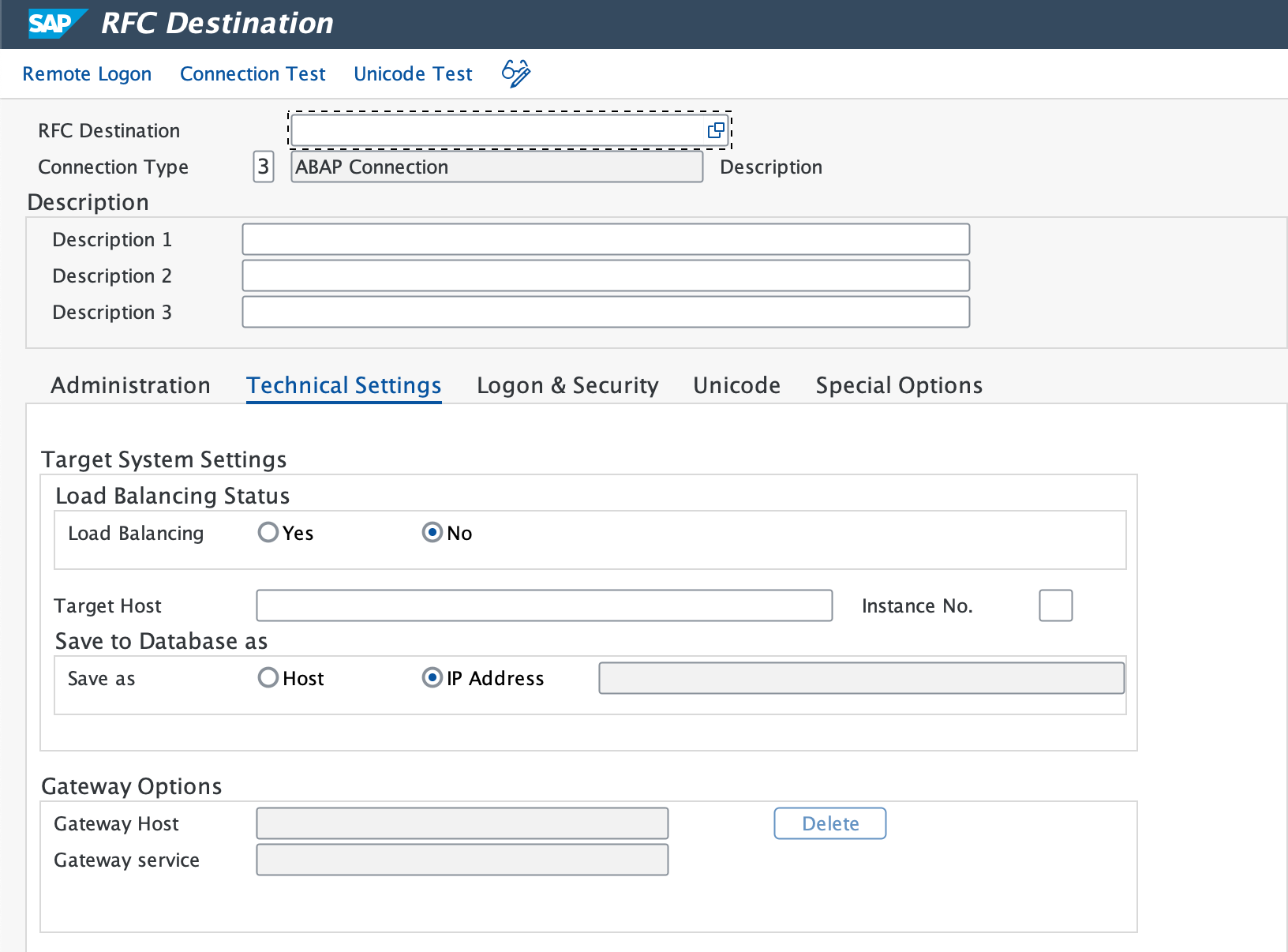
Logon & Securityタブで、RFC user(
NR4SAPDP)とパスワードを入力します。Saveを選択します。
Utility > Test > Connection Testに移動し、次にAuthorization Testに移動します。
- Expected result: 両方のテストで成功ステータスが示されています。
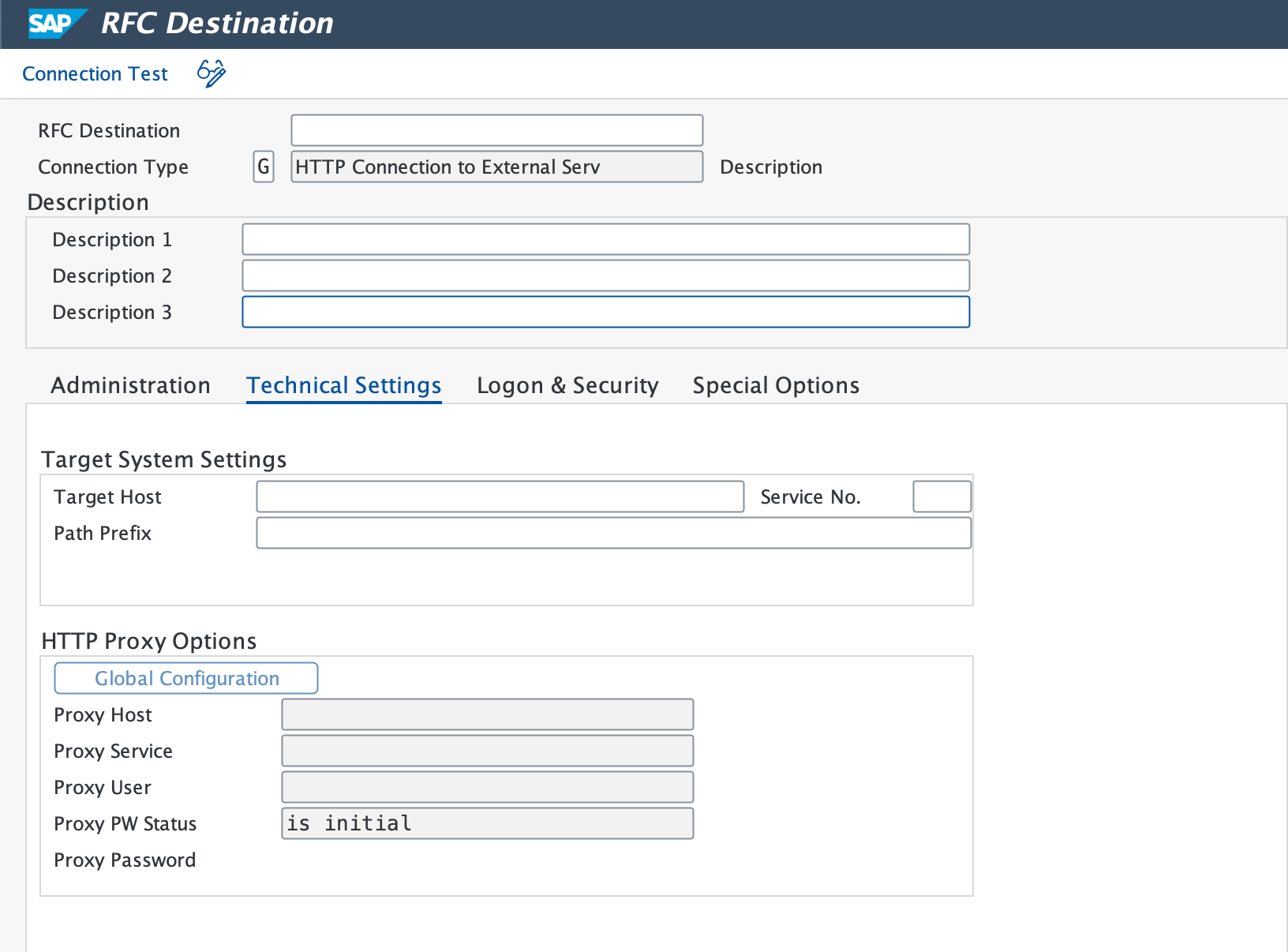
HTTP宛先をNew Relic cloudに設定する
トランザクションSM59を使用して、HTTPS connectionsをNew Relic API endpointsに設定します。
重要
Events、Logs、Metrics、およびTracesに対して、個別のRFC destinationsを別々に作成します。
Destination Nameを入力します (例:
NR_API_EVENT)。Connection Typeを
G(外部サーバーへの HTTP 接続) に設定します。Target Host、Service No.に443(HTTPSの標準ポートを参照)、およびPath Prefix(詳細については、インストレーション準備チェックリストを参照)を入力します。
プロキシが必要な場合は、Technical Settingsタブで設定します。
Security Optionsタブで、SSLのActiveオプションを選択します。
必要に応じて、New Relicからroot certificateをダウンロードし、トランザクション
STRUSTを使用してSAPに追加します。Connection Testを選択して接続を確認します。
- Expected result: 接続が成功すると、ログオンデータの入力を求めるプロンプトが表示されます。
- If test times out: ファイアウォールの設定を確認してください。
すべてのNew Relic API endpointsに対してこの手順を繰り返します。
BTP/CloudALM認証エンドポイントを作成する
サービスに応じて以下の手順に従ってください。
ダウンロードしたService Keyの
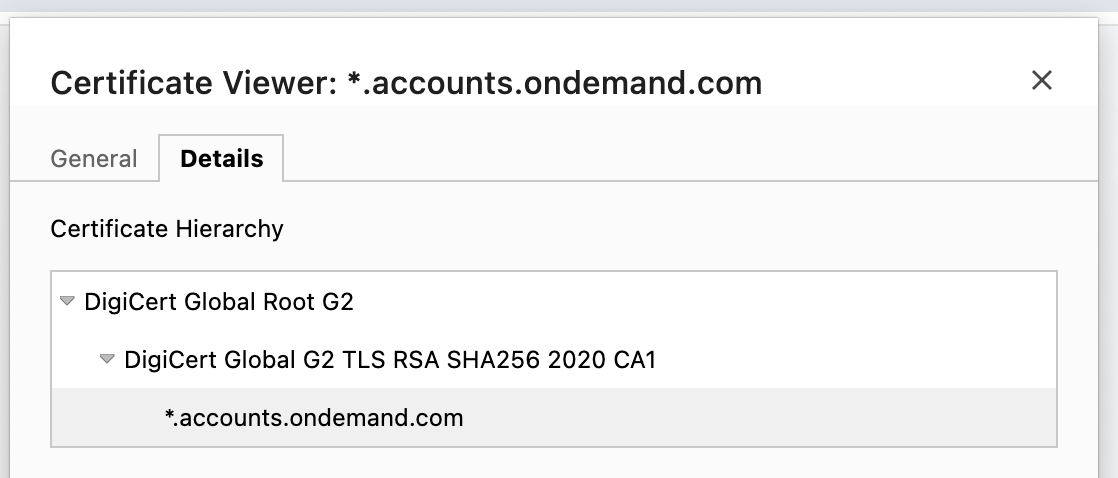
clientId、clientsecret、tokenurlをメモします。Web ブラウザーで
tokenurlにアクセスし、必要な証明書(Digicert root、global、およびSAP on demand)をダウンロードします。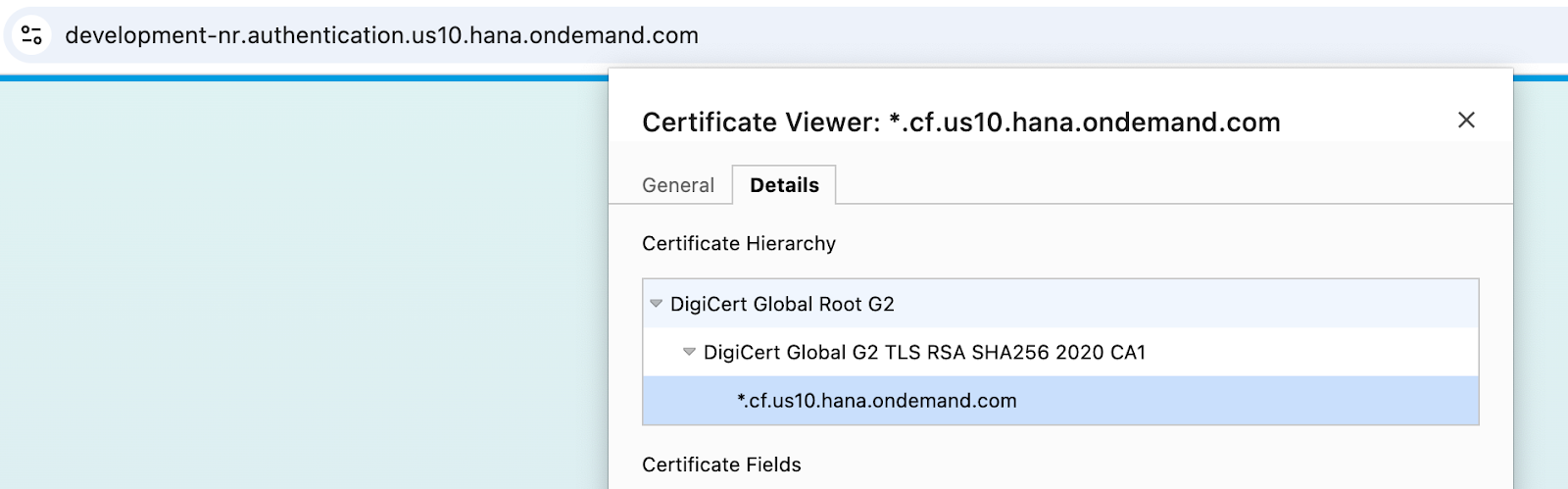
トランザクション
STRUSTを使用して3つの証明書を1つずつアップロードし、次にAdd to Certificate Listを選択します。Saveを選択します。
トランザクション
SMICMを使用して、Administration > ICM > Exit Soft > Globalに移動し、すべてのICM processesを再起動します。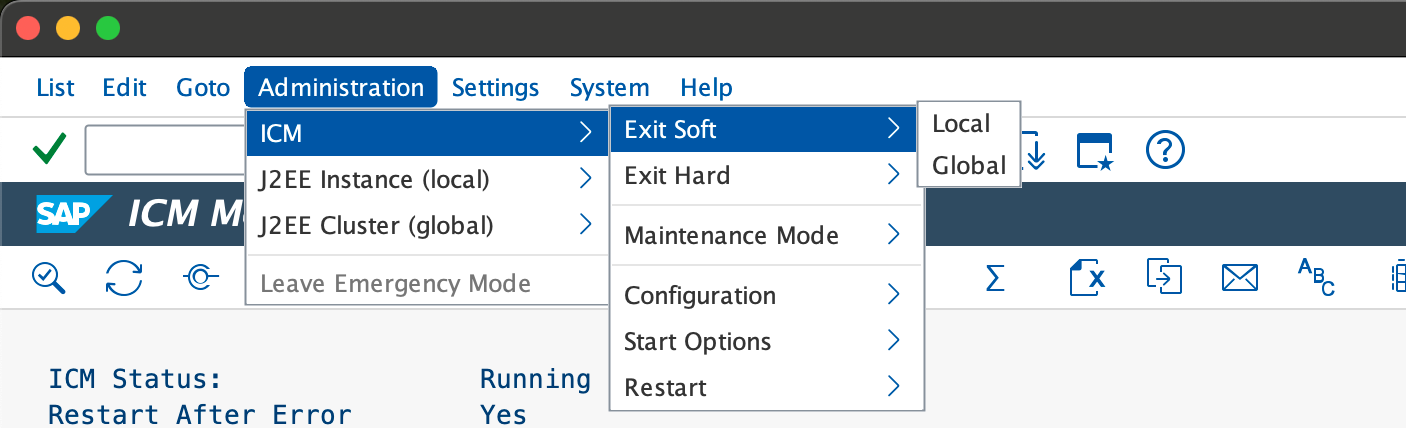
トランザクション
SM59を使用して、HTTP Connections to External Serverの下に新しいRFC connectionを作成します。tokenurlをホストとパスプレフィックスに分割し、パスプレフィックスに
?grant_type=client_credentialsを追加します。Service No.を
443に設定します。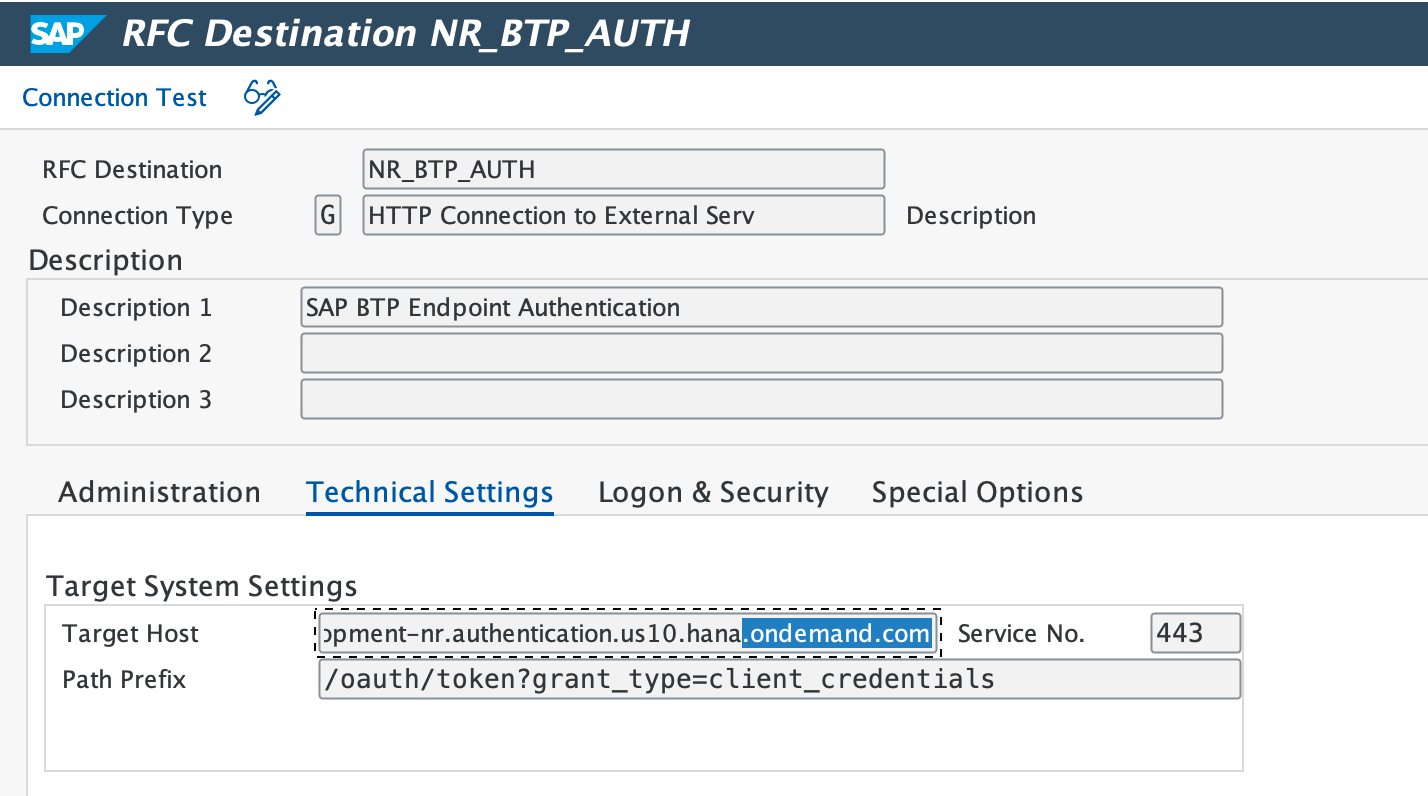
Login & SecurityタブでBasic Authenticationを選択し、ユーザー名とパスワードとして
clientIdとclientsecretを入力します。Secure ProtocolのステータスをActiveに設定し、設定を保存します。
Connection Testを選択します。
ダウンロードしたService Keyの
clientId、clientsecret、urlをメモします。Web ブラウザーでurlにアクセスし、Digicert root、global、およびSAP on demandの証明書をダウンロードします。
トランザクション
STRUSTを使用して3つの証明書を1つずつアップロードし、次にAdd to Certificate Listを選択します。Saveを選択します。
トランザクション
SMICMを使用して、Administration > ICM > Exit Soft > Globalに移動し、すべてのICM processesを再起動します。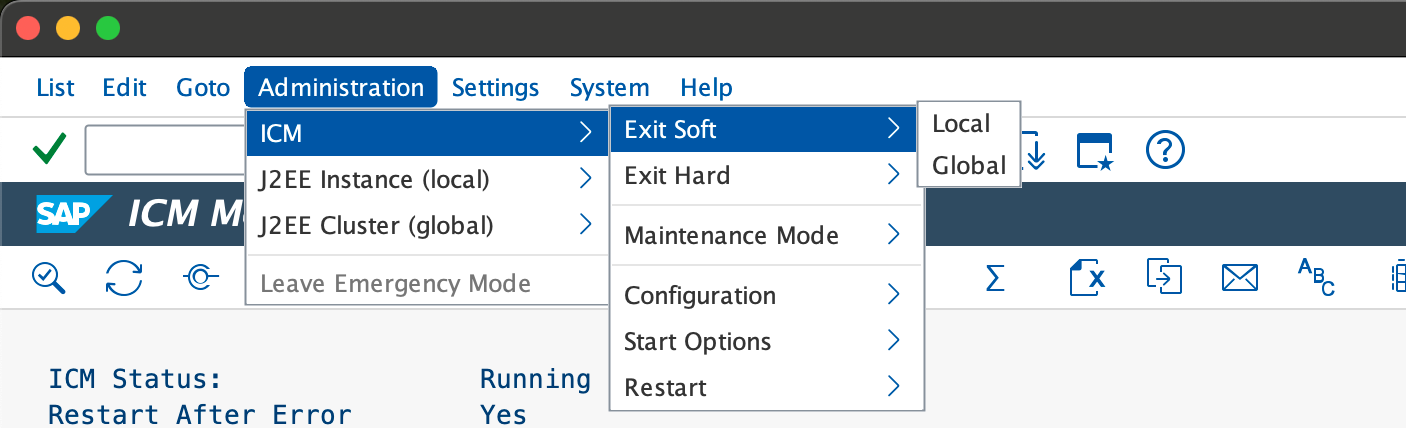
トランザクション
SM59を使用して新しいRFC connectionを作成します。urlをTarget hostとして入力し、Service No.を
443に設定します。Path Prefixを/oauth/token?grant_type=client_credentialsに設定します。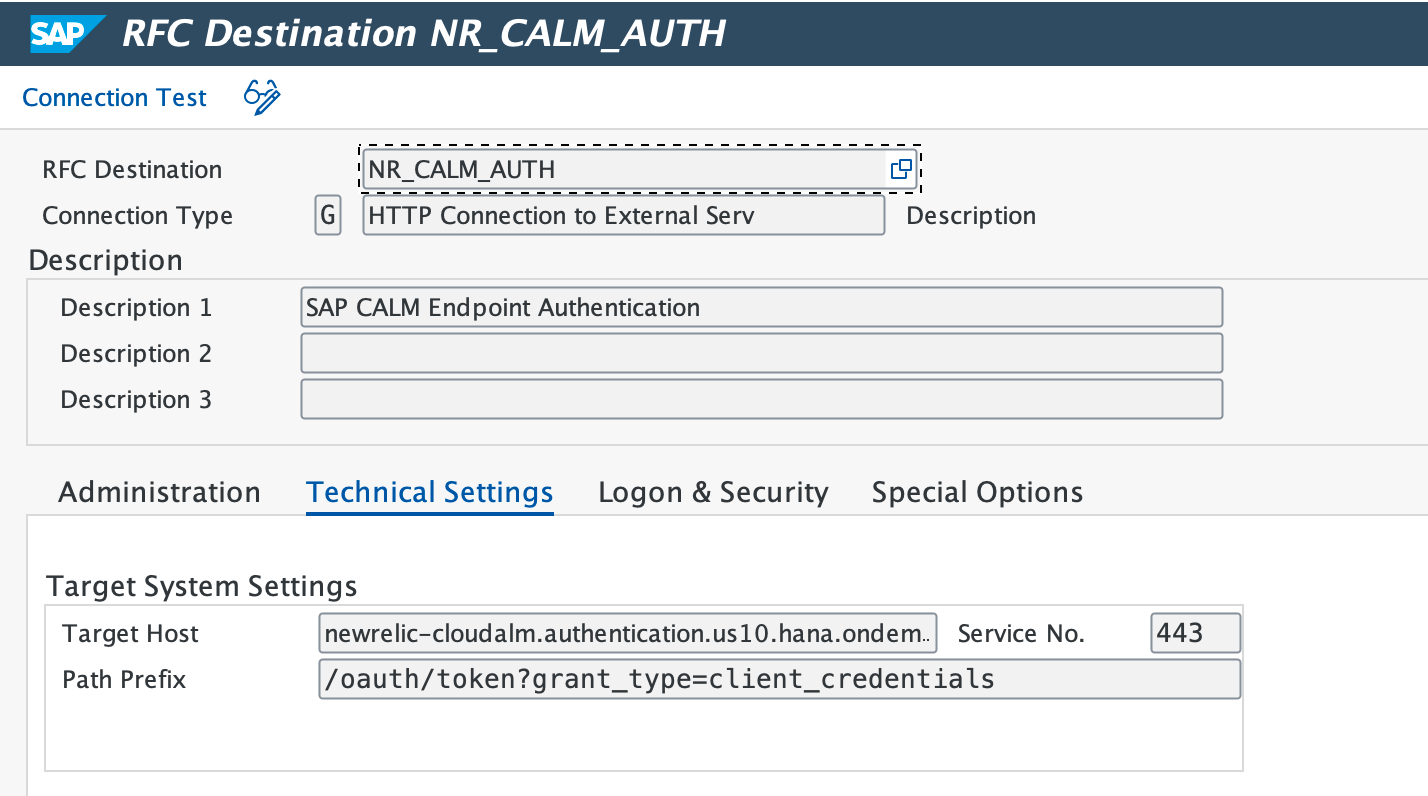
Login & SecurityタブでBasic Authenticationを選択し、ユーザー名とパスワードとして
clientIdとclientsecretを入力します。Secure ProtocolのステータスをActiveに設定し、設定を保存します。
Connection Testを選択します。
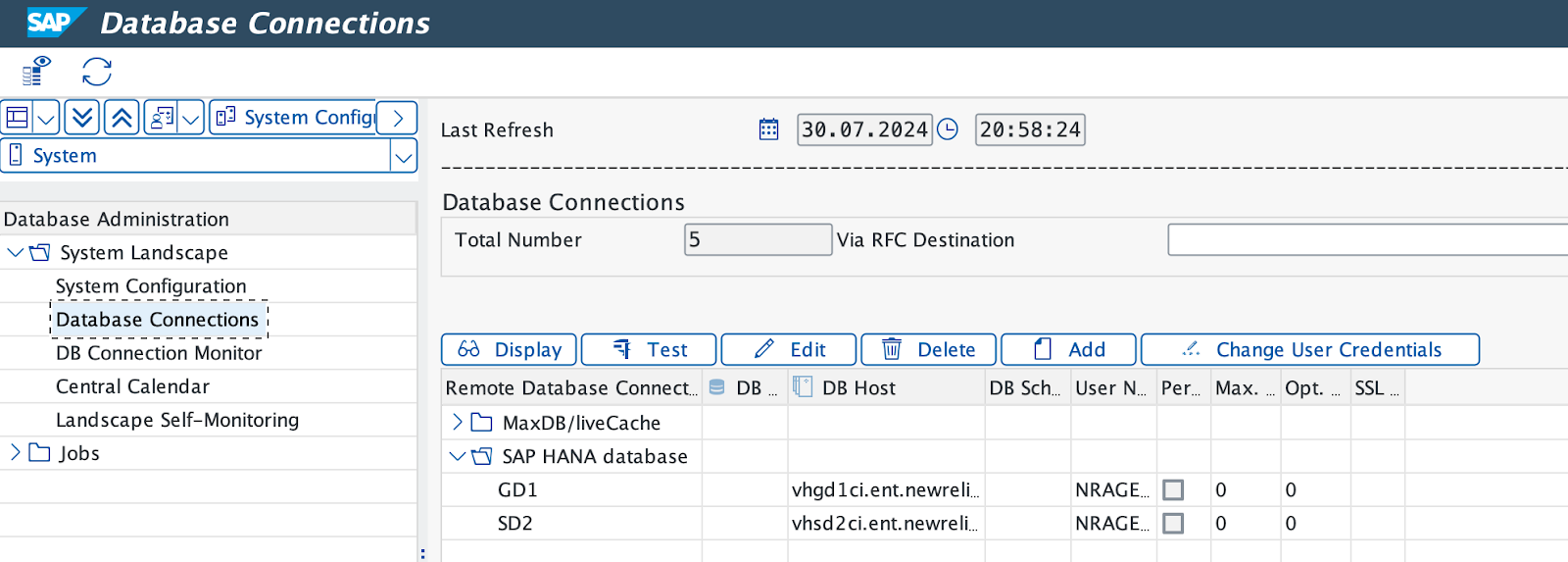
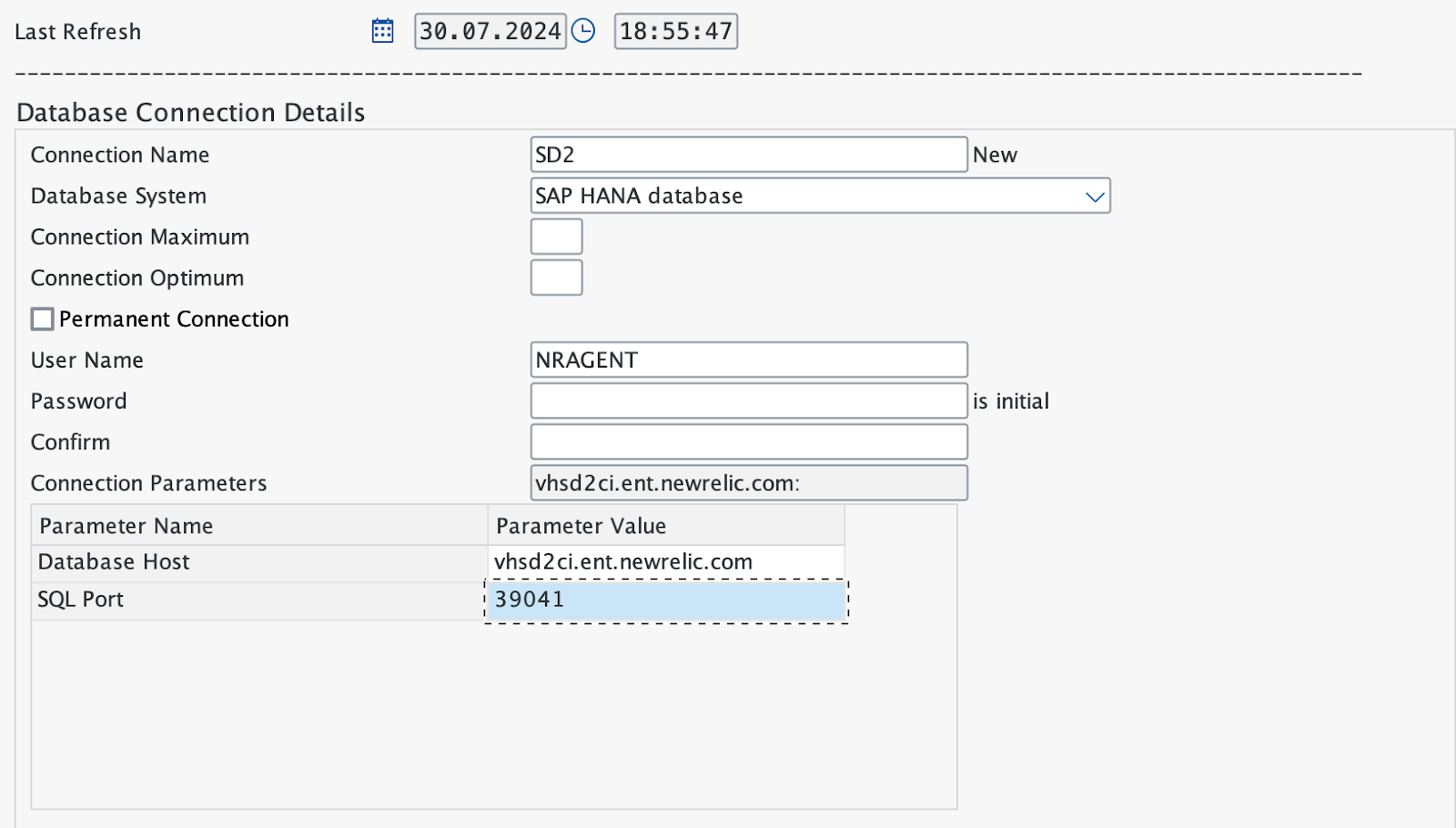
データベース接続を作成する
トランザクションDBACOCKPITを使用して、リモートHANA Database connectionsを定義します。